What is Application Security?
Effective Security Testing Safeguards your Applications from Cyber Threats & Vulnerabilities
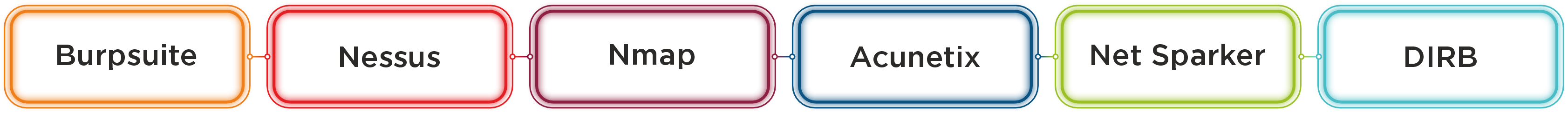
Armorize’s Application Security Testing helps you detect application vulnerabilities, provide full coverage for Web and Mobile application infrastructure and online services, and reduce risks to meet regulatory compliance requirements. Our Application Security Methodology extends beyond scanning software detection to identify and prioritize the most vulnerable aspects of your online application, as well as come up with practical Solutions.